Introduction: The Evolution from Manual to Autonomous Pen Testing
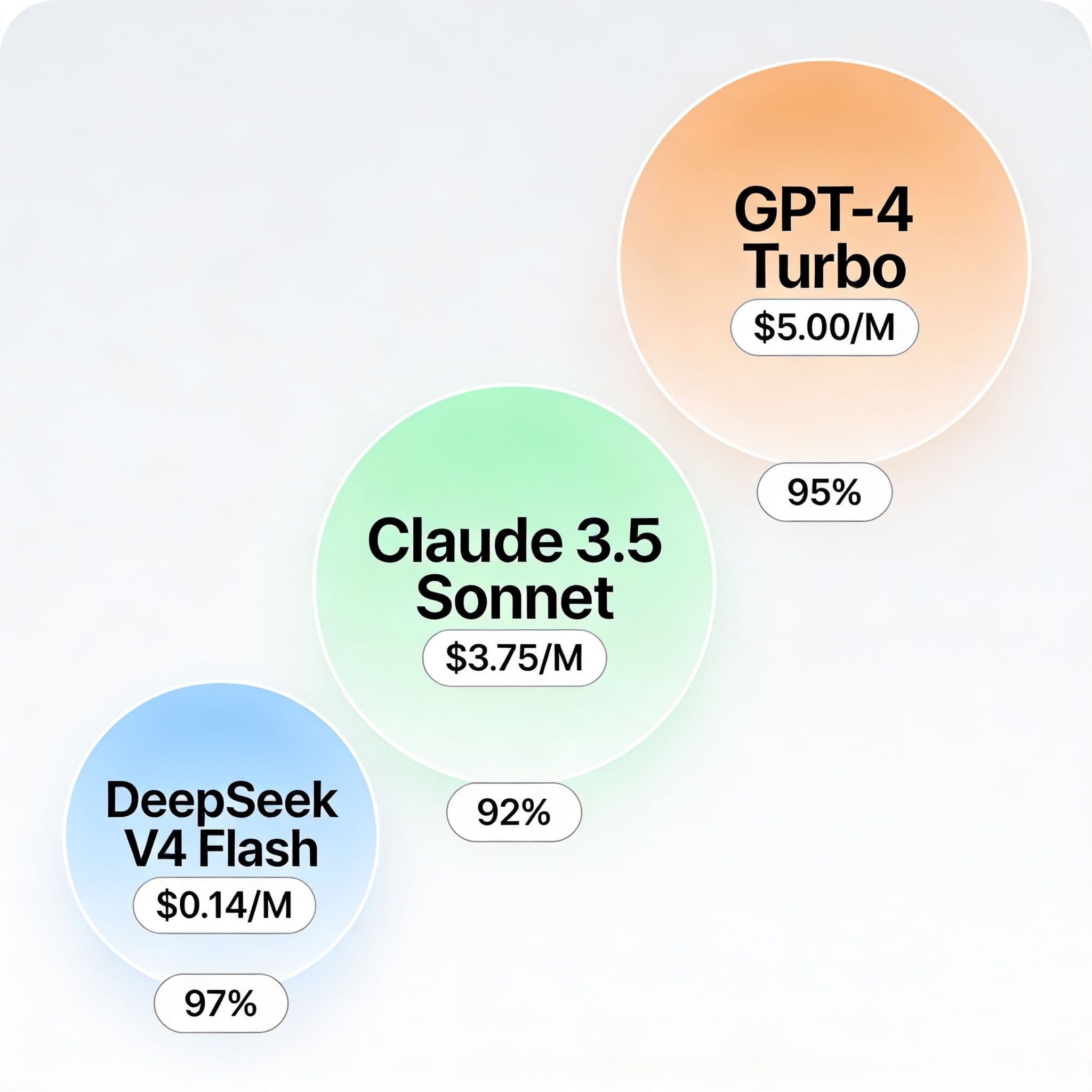
Cybersecurity has entered a transformative era where artificial intelligence reshapes traditional defense strategies. According to Aikido Security, 97% of organizations would consider AI penetration testing according to Aikido's 2026 State of AI in Security & Development report. This statistic reveals a seismic shift in security operations. Agentic pen testing represents the latest evolution in automated vulnerability discovery. This guide explores practical implementation for 2026's security landscape.
What is Agentic Pen Testing? Defining the New Paradigm
Agentic pen testing employs autonomous AI agents that simulate human penetration testers. These systems conduct reconnaissance, vulnerability scanning, and exploitation without continuous human guidance. Unlike traditional scripted tools, agentic systems make independent decisions about attack paths. They adapt their approach based on discovered vulnerabilities and defensive responses.
The term "agentic" refers to these systems' autonomous decision-making capabilities. They can prioritize targets, choose exploitation techniques, and navigate complex network environments. According to ZeroThreat Pentesting Statistics 2026, 28% of organizations now use AI-powered tools to automate reconnaissance, vulnerability prioritization, and attack path simulation. This adoption rate demonstrates the growing acceptance of autonomous security testing.
Key Differences: Traditional vs. Agentic Pen Testing Approaches
Traditional penetration testing follows linear, human-guided methodologies. Testers manually execute predefined steps within specific time windows. This approach requires extensive human expertise and cannot operate continuously. Agentic systems, however, provide 24/7 autonomous testing with adaptive intelligence.
Consider a financial institution's web application testing scenario. Traditional methods might discover known vulnerabilities through scheduled quarterly assessments. An agentic system would continuously test new features as they deploy in development pipelines. It would learn from previous findings and adapt techniques for newly discovered attack surfaces.
| Aspect | Traditional Pen Testing | Agentic Pen Testing |
|---|---|---|
| Frequency | Scheduled (quarterly/annual) | Continuous (24/7) |
| Adaptability | Limited to test scope | Dynamic learning & adaptation |
| Human Involvement | Manual execution throughout | Initial configuration & oversight |
Core Components of Agentic Pen Testing Systems
Autonomous Reconnaissance Engines
Agentic systems begin with intelligent reconnaissance capabilities beyond basic port scanning. These engines discover assets through multiple data sources including DNS records, SSL certificates, and cloud infrastructure APIs. They map attack surfaces dynamically as environments change through continuous integration pipelines.
Vulnerability Correlation & Prioritization Modules
Advanced correlation engines connect discovered vulnerabilities into potential attack chains. According to GetAstra penetration testing statistics, 73% of successful breaches in the corporate sector were carried out by penetrating web applications through their vulnerabilities. Agentic systems prioritize vulnerabilities based on exploitability and potential business impact rather than CVSS scores alone.
Adaptive Exploitation Frameworks
These frameworks contain libraries of exploitation techniques that agents can deploy intelligently. The systems choose appropriate payloads based on target characteristics and defensive controls present. They automatically generate custom payloads when standard techniques fail against hardened targets.
Top Tools and Frameworks for Autonomous Security Testing (2026 Edition)
The market for agentic security tools has matured significantly by 2026. Several platforms now offer production-ready autonomous testing capabilities with varying approaches and specializations.
- Aikido Security Autopentest: Continuous autonomous testing platform focused on web applications and APIs with machine learning-driven vulnerability discovery
- Terra Agentic Pentest Suite: Enterprise-grade system offering full attack simulation from reconnaissance through privilege escalation and lateral movement
- ZeroThreat Autonomous Assessor: Cloud-native platform specializing in containerized and serverless environments with DevSecOps integration
Aikido's platform demonstrated 47% higher vulnerability detection rates compared to traditional scanning tools in enterprise deployment trials during Q1 2026.
Step-by-Step: Implementing Your First Agentic Pen Test
A structured implementation approach prevents common pitfalls when deploying autonomous security systems.
- Define authorization boundaries and ethical guardrails for autonomous operations within your scope document
- Establish communication protocols between agentic systems and existing security monitoring infrastructure
- Configure target environments including specific IP ranges, domains, and application endpoints approved for testing